Critical Security Issues Might Affect Many HP Printers
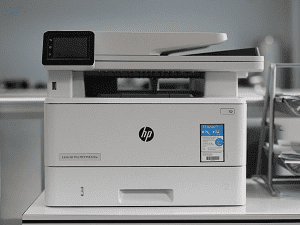
Do you have an HP LaserJet Pro, a Pagewide Pro, an OfficeJet, Enterprise, Large Format, or DeskJet printer at your home or in your office?
If so, then be aware that your machine is likely vulnerable to at least one of four security vulnerabilities rated as critical.
The first of these is a buffer overflow flaw that could lead to remote code execution. Tracked as CVE-2022-3942, this issue was originally reported by Trend Micro’s Zero Day Initiative team.
The other vulnerabilities to be aware of are tracked as follows:
- CVE-2022-24291
- CVE-2022-24292
- And CVE-2022-24293
All also reported by Trend Micro’s Zero Day Initiative Team.
Although the team that discovered the flaws haven’t provided many details about them, the good news is that HP has already released a security patch for the firmware of all the impacted printers. Just head to HP’s driver download portal, select the make and model of your printer, and grab the appropriate firmware update for your machine and you’ll be all set.
All the issues mentioned here are as serious as they get. All will allow an attacker to gain a foothold inside your home or office network and execute code at will. If they do that, you can bet that it won’t be to your benefit so it pays to update your firmware as quickly as possible to mitigate your risk.
Kudos to the researchers at Trend for spotting these vulnerabilities, and to HP for moving quickly and decisively to protect their vulnerable customers. This could have played out very differently given how many makes and models of HP printers were impacted by this quartet of security flaws.
Thanks to the company’s quick action though it seems that much of the potential impact has been blunted at least for those who move quickly to update their firmware. That’s how it’s done.